51% Attacks Explained: How Blockchains Get Rewritten
51% Attacks are one of the clearest ways to understand how blockchain security really works. 51% Attacks do not break private keys, but they can break trust in transaction history. When 51% Attacks succeed, an attacker can reverse recent payments, trigger deep chain reorganizations, and exploit exchanges or merchants that assume a transaction is already final.
For anyone researching blockchain risk, this matters because the real danger behind 51% Attacks is not just technical. It is economic. A chain is only as secure as the cost of overpowering its consensus. In this guide, you will learn what 51% attacks are, how they work, what attackers can and cannot do, and why some blockchains are far more exposed than others.
What Are 51% Attacks?
A 51% attack happens when one miner, validator set, or coordinated group controls enough consensus power to influence which version of the blockchain becomes the accepted history. In Proof of Work networks, that usually means controlling a majority of hash power. In other consensus systems, the threshold for disruption may differ, but the principle stays the same: one actor gains enough influence to undermine honest participants.
In practice, 51% attacks are usually associated with chain reorganizations. The attacker secretly builds an alternative version of the chain while the public network continues operating normally. If the attacker’s private chain becomes heavier or longer under the protocol’s rules, the network may accept it as canonical. That is where recent transactions can be erased or replaced.
This is why 51% attacks are so dangerous for exchanges, payment processors, and merchants. A transaction may look confirmed, yet still be vulnerable if the network’s finality is weak and the attacker can outpace honest block production.
How 51% Attacks Work in Crypto
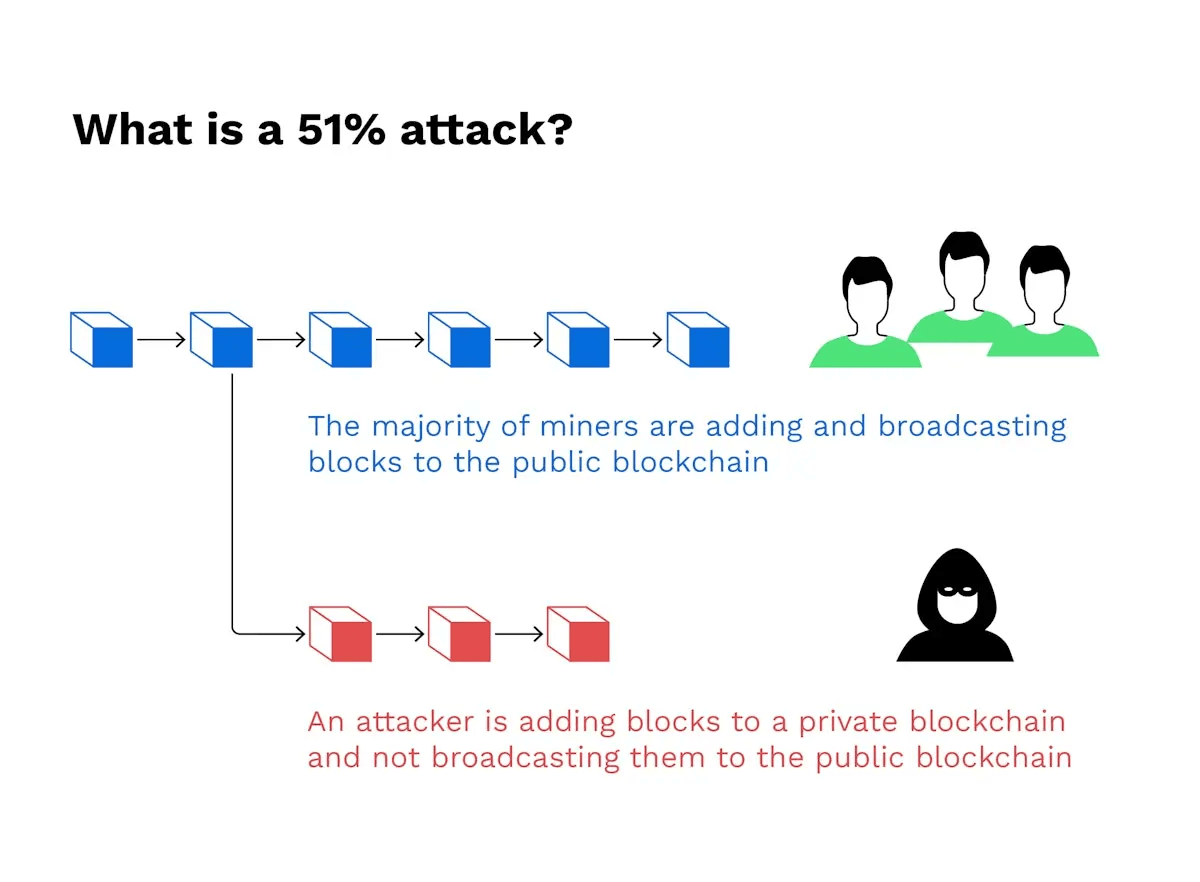
The classic attack path is a double-spend.
First, the attacker sends coins to an exchange or merchant. The transaction enters the public chain and receives the required confirmations. Once the platform credits the deposit, the attacker trades the funds for another asset or withdraws value elsewhere.
At the same time, the attacker privately mines or validates a competing chain that excludes the original payment. Because the attacker controls the majority of consensus power, this hidden chain can eventually overtake the public one. Once the attacker has already extracted value, they publish the private chain. Honest nodes then follow the protocol rules and accept the stronger chain, while the original deposit disappears from canonical history.
The result is simple but severe: the exchange or merchant loses value, and the attacker keeps the proceeds.
This also explains why 51% attacks are often described as consensus attacks rather than wallet hacks. The attacker is not stealing your private key. The attacker is rewriting the order of transactions the network agrees to recognize.
What 51% Attacks Can and Cannot Do
A successful attacker can:
- Reverse their own recent transactions
- Delay or censor new transactions
- Trigger deep chain reorganizations
- Undermine settlement confidence on weaker chains
A successful attacker usually cannot:
- Steal coins from wallets they do not control
- Forge signatures for another user
- Mint unlimited coins outside protocol rules
- Freely rewrite finalized history in networks with strong finality defenses
That distinction is critical. Many newer users hear “51% attacks” and assume attackers can drain any wallet on the network. That is not how this threat works. The real damage comes from broken finality, not broken cryptography.
Why Smaller Chains Face Higher 51% Attack Risk
Not every blockchain faces the same exposure. Large networks with massive, globally distributed mining or staking power are much harder to attack. Smaller networks, especially minority Proof of Work chains, often carry far more risk.
One reason is the rise of hash-rental markets. Attackers do not always need to own mining hardware outright. If enough hash power can be rented for a short period, the cost of launching 51% attacks falls dramatically. That makes smaller chains with lower security budgets much easier to exploit.
Historical cases show this clearly.
Targeted Network | Attack Period | Exploited Value (Estimated) | Attack Vector and Operational Notes |
Bitcoin Gold (BTG) | May 2018 | ~$18 Million | Double-spend targeting exchanges via massive rented hash power, utilizing wallet GTNjvCGssb2rbLnDV1xxsHmunQdvXnY2Ft. |
Ethereum Classic (ETC) | January 2019 | ~$1.1 Million | Successful double-spend through deep chain reorganization. |
Expanse (EXP) | July 2019 | Undisclosed | Detected via deep reorg tracking monitoring systems. |
Litecoin Cash (LCC) | July 2019 | Undisclosed | Chain reorganization detected exceeding 6 blocks deep. |
Vertcoin (VTC) | December 2019 | Undisclosed | 51% attack resulting in deep chain reorganization and network disruption. |
Bitcoin Gold (BTG) | Jan/Feb 2020 | ~$70,000+ | Secondary attack exposing the continued vulnerability of the network. |
Ethereum Classic (ETC) | August 2020 | ~$5.6 Million | Coordinated DaggerHashimoto rental via NiceHash; targeting OKEX. |
Why 51% Attacks Are Not the Whole Story
The phrase “51% attacks” is useful, but it can oversimplify the real security model.
Research on selfish mining shows that attackers may not always need a full majority to distort network incentives. By withholding blocks and strategically releasing them, a coordinated mining group can waste honest miners’ work and gain an unfair advantage. Under some conditions, this creates centralization pressure long before a full majority is reached.
Modern blockchain security therefore depends on more than just one number. It depends on network propagation, miner or validator distribution, economic incentives, and how finality is enforced.
That is why newer systems increasingly rely on stronger finality mechanisms. In Proof of Stake and BFT-style designs, deep rollbacks can become far more costly because they require slashable behavior, supermajority failure, or direct economic loss. Some networks also use anti-reorg systems and checkpoint-based defenses to reduce the attacker’s payoff window.
The big takeaway is this: 51% attacks reveal whether a network has real security depth or only superficial decentralization.
How to Evaluate a Blockchain’s Defense Against 51% Attacks
If you are evaluating a chain, ask these questions:
- How expensive is it to control enough consensus power to disrupt the network?
- Can that power be rented cheaply from outside markets?
- Does the chain rely only on probabilistic confirmations, or does it have stronger finality?
- How concentrated are miners or validators?
- How do exchanges and infrastructure providers handle reorg risk?
These questions matter more than marketing language. A blockchain may promise speed, low fees, or accessibility, but if its consensus can be cheaply overwhelmed, those benefits come with a real tradeoff.
Conclusion
51% Attacks remain one of the most important concepts in blockchain security because they expose the gap between apparent confirmation and true finality. 51% Attacks do not let someone break your wallet keys, but they can let attackers reverse payments, exploit exchanges, and rewrite recent chain history when consensus becomes too concentrated or too cheap to control.
If you want to assess crypto risk seriously, do not just ask whether a chain is popular. Ask how it handles reorganizations, how expensive majority control really is, and what defenses stand between honest users and successful 51% Attacks. That is where blockchain trust is either earned or exposed.
Learn more about consensus design, finality, and exchange risk before you rely on any blockchain for serious value transfer.
FAQ
Q1:What are 51% attacks in simple terms?
51% attacks happen when one actor controls enough consensus power to influence which blockchain history the network accepts as valid.
Q2:Can 51% attacks steal funds from my wallet?
Not directly. They usually cannot steal coins from a wallet without the private key, but they can reverse recent transactions and disrupt settlement.
Q3:Which blockchains are most vulnerable to 51% attacks?
Smaller Proof of Work chains are often more exposed, especially when hash power can be rented cheaply from external markets.
Q4:Are Proof of Stake networks immune to 51% attacks?
No. They change the attack model, but they are not automatically immune to censorship, disruption, or finality-related attacks.
Q5:Why do exchanges care so much about 51% attacks?
Because exchanges can lose money if a deposit appears confirmed, gets credited, and is later erased by a chain reorganization.
